Reassessing Private Key Management in the Context of Mainstream Cryptocurrency Adoption
At the Consensus 2026 conference, Charles Hoskinson, the founder of Cardano, articulated a paradigm shift in the management of private keys within cryptocurrency ecosystems. He posited that “users should probably never have their private keys,” suggesting that key management should be delegated to secure systems capable of safeguarding these cryptographic secrets. This assertion underscores an evolving discourse surrounding user experience and security in cryptocurrency, particularly as it pertains to retail adoption.
The Inherent Challenges of Private Key Management
Private key management has long served as a significant bottleneck impeding widespread retail adoption of cryptocurrencies since the inception of Bitcoin. Users often grapple with the complexities associated with their 12- or 24-word seed phrases, resulting in frequent occurrences of:
– Forgetfulness
– Insecure storage practices (e.g., photographing seed phrases)
– Cloud-based mismanagement
– Complete loss of access
The emergence of hardware wallets such as Ledger and Trezor represented a critical step toward alleviating these challenges by generating and storing keys in a manner that prevents exposure in plaintext form. However, this solution has also introduced friction that mainstream users frequently reject, thereby limiting broader acceptance.
Technological Advancements in Secure Credential Management
Recent reports from FIDO revealed that there are currently approximately 5 billion active passkeys globally, with an impressive 75% of consumers having enabled at least one form of this authentication method. It is evident that users are increasingly comfortable with device-bound, biometric-unlocked credentials as a normative aspect of authentication processes.
Coinbase has operationalized this trend through its smart wallet feature, which allows users to onboard without requiring a recovery phrase. Instead, it utilizes Apple or Google passkeys to create non-exportable credentials that are intrinsically bound to secure hardware. This innovative approach simplifies user interaction by relying solely on Face ID or a PIN for authentication.
The Security Architecture of Mainstream Mobile Devices
Hoskinson’s assertions regarding the security capabilities embedded within mainstream mobile devices merit further exploration. Apple’s Secure Enclave represents a dedicated subsystem designed to isolate sensitive data from potential threats posed by compromised application processors. Similarly, Android’s Keystore system employs hardware-backed keys that maintain non-exportability while binding them to a Trusted Execution Environment (TEE) or secure element. The implementation of StrongBox further enhances security through additional isolation requirements.
Moreover, Samsung’s Knox framework offers robust hardware-backed key protection via TrustZone technology, supplemented by DualDAR encryption layers specifically for managing work profile data. Hoskinson described the Knox work profile as embodying “a separate operating system, separate circuits in the hardware,” signifying a heightened level of security architecture.
### Comparative Analysis: Wallet Models
| Model | Key Location | Key Extractability | Malware Vulnerability | Transaction Verification | Optimal Use Case |
|——————————–|———————————————————–|————————|—————————-|——————————————|———————————————————|
| **Seed Phrase Wallet** | Derived from a 12- or 24-word recovery phrase | Yes | Yes | Via wallet app interface | Low-friction onboarding; suitable for small balances |
| **Phone-Based Hardware Wallet**| Within device’s secure hardware (Apple Secure Enclave) | Generally no | Yes | Through phone UI and prompts | Everyday payments; routine self-custody |
| **Dedicated Hardware Wallet** | Within standalone signing devices (Ledger/Trezor) | Generally no | Much harder | On trusted display | Larger balances; long-term storage for security-conscious users |
Evaluating the Advantages of Dedicated Wallets
The operational dynamics between phone-based secure hardware and dedicated signing devices are informed by distinct threat models. For instance, Ledger’s secure element incorporates a secure display on the device itself, enabling users to verify transaction details even if the connected phone or computer is compromised. Trezor’s trusted display similarly allows users to view transaction details independent of potentially malicious host machine displays; recent models have integrated secure elements to address previous critiques regarding their security architecture.
However, Hoskinson aptly identified accessibility as a challenge inherent in using dedicated devices like Ledger and Trezor. These wallets necessitate separate devices, companion applications, and signing workflows that may disrupt user experience. Conversely, mobile phones present viable alternatives for everyday transactions and routine self-custody.
The integration of artificial intelligence (AI) into payment systems introduces additional complexity regarding transaction authority and user consent. While AI agents necessitate payment authority for operational efficacy, granting such agents access to master private keys poses substantial risks that most users would instinctively reject.
The Architecture for Bounded Delegation
A promising approach involves establishing bounded delegation models whereby an agent is authorized to execute transactions within predefined limits without direct access to master credentials. Coinbase’s AgentCore Payments integration exemplifies this model by facilitating transactions under budget controls while maintaining comprehensive audit trails without exposing private-key access.
Ethereum’s EIP-4337 has catalyzed the creation of over 26 million smart wallets and 170 million UserOperations, providing frameworks for programmable wallet behavior extending to externally owned accounts. This capability enables features such as batching transactions, gas sponsorships, recovery mechanisms, and customized control settings.
The underlying infrastructure supporting permission-based and agent-compatible wallets is already gaining traction at a significant scale.
Revisiting Self-Custody Philosophies
The adage “not your keys, not your coins” embodies both philosophical and technical dimensions pertaining to cryptographic custody. Nonetheless, this framework may falter under the demands of mass-market distribution. A more sustainable model for self-custody may evolve into biometric-based authentication systems that generate non-exportable keys within secure hardware environments—thereby circumventing user interactions with raw cryptographic material altogether.
In practical application, users would wield control over spending limits, session keys, delegated authorizations, recovery protocols, and intuitive approval workflows.
Apple’s secure intent mechanism exemplifies a robust framework allowing hardware to confirm user intent in ways that even root or kernel-level software cannot compromise. Android’s Keystore further supports per-operation authentication requirements, shifting custody paradigms from “can you keep a secret?” towards “can you verify what you meant to authorize?”
However, it is paramount to recognize that while non-extractability provides safeguards against unauthorized access to hardware-backed keys, it does not inherently guarantee transaction security. Notable incidents—such as CertiK’s analysis of the Bybit incident—highlight how attackers can exploit vulnerabilities in approved transactions even when private keys remain secured in hardware environments.
Projecting Future Trajectories
If wallet interfaces effectively address user intent through standardized spending caps and clear approval prompts conducive to consumer trust, there exists potential for phone-primary self-custody solutions to capture between 70% and 85% of new retail users by 2028. This scenario would render seedless onboarding as the norm while establishing account abstraction as an expectation rather than an advanced feature.
Conversely, if incidents involving mobile signing vulnerabilities—such as phishing attacks and compromised approval flows—continue unabated leading to high-profile losses among users, phone-based self-custody may stagnate at merely 20% to 35% market penetration. Users faced with financial losses attributed to mobile wallet manipulations often perceive these events as hacks and revert their activities back to centralized exchanges.
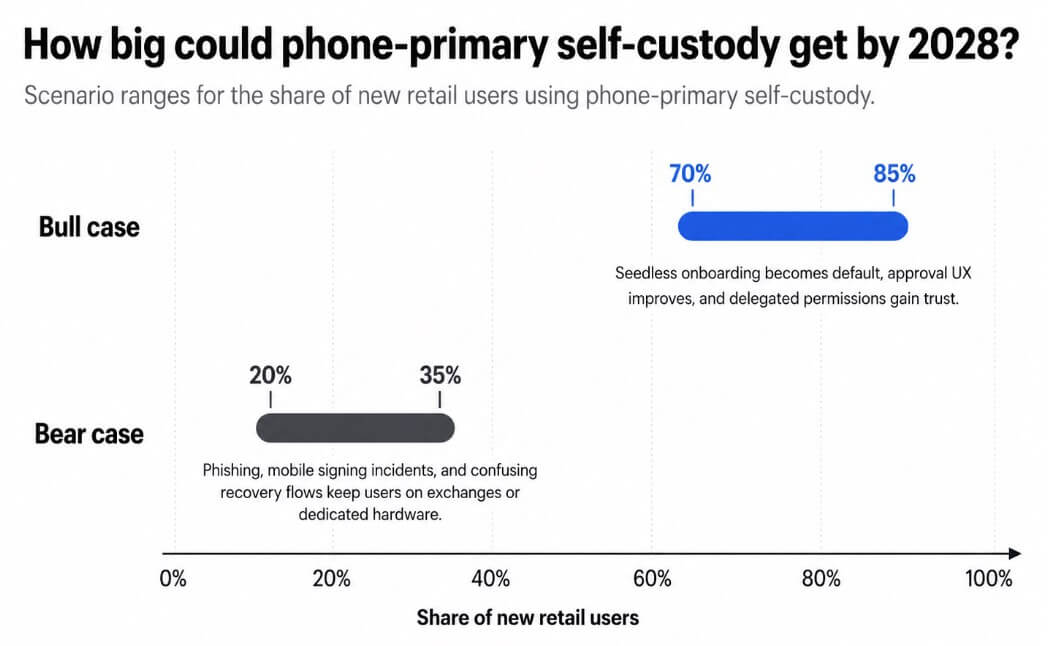
*Figure: A scenario chart projects phone-primary self-custody reaching between 70% and 85% market share among new retail users by 2028 under favorable conditions versus only 20% to 35% under adverse conditions.*
Underpinning either trajectory is an uncomfortable reality concerning platform dependency. Should self-custody transition into hardware embedded within smartphones—effectively placing Apple, Google, Samsung, and major wallet SDK providers at pivotal junctures within crypto’s security architecture—the model may retain its non-custodial nature on a technical level yet become increasingly reliant on operating system APIs and app distribution frameworks for its overall security integrity.