preferred on
Apple Inc. is poised to undergo a significant leadership transition, coinciding with increasing scrutiny regarding the security of its App Store and the alarming rise in cryptocurrency thefts affecting iPhone users.
Leadership Transition: A New Era for Apple
On April 20, Apple announced the impending succession of Tim Cook as Chief Executive Officer (CEO) by John Ternus, currently serving as Senior Vice President of Hardware Engineering, effective September 1. Following this transition, Cook will assume the role of Executive Chairman.
Ternus’s elevation to CEO is underscored by his extensive experience within Apple’s product ecosystem. Since his induction into the company, he has significantly contributed to the development of critical products including the iPad, AirPods, iPhone, and Mac. Notably, he spearheaded Apple’s strategic transition to proprietary silicon for Mac devices and recently unveiled the iPhone Air.
Tim Cook extolled Ternus’s capabilities, stating:
“John Ternus has the mind of an engineer, the soul of an innovator, and the heart to lead with integrity and with honor. He is a visionary whose contributions to Apple over 25 years are already too numerous to count, and he is without question the right person to lead Apple into the future.”
Challenges Confronting Apple’s New Leadership
The forthcoming leadership transition occurs against a backdrop of multifaceted pressures confronting Apple. These include:
– Intensifying competition in artificial intelligence.
– A deceleration in hardware growth.
– An emergent security challenge within one of its most closely monitored business segments.
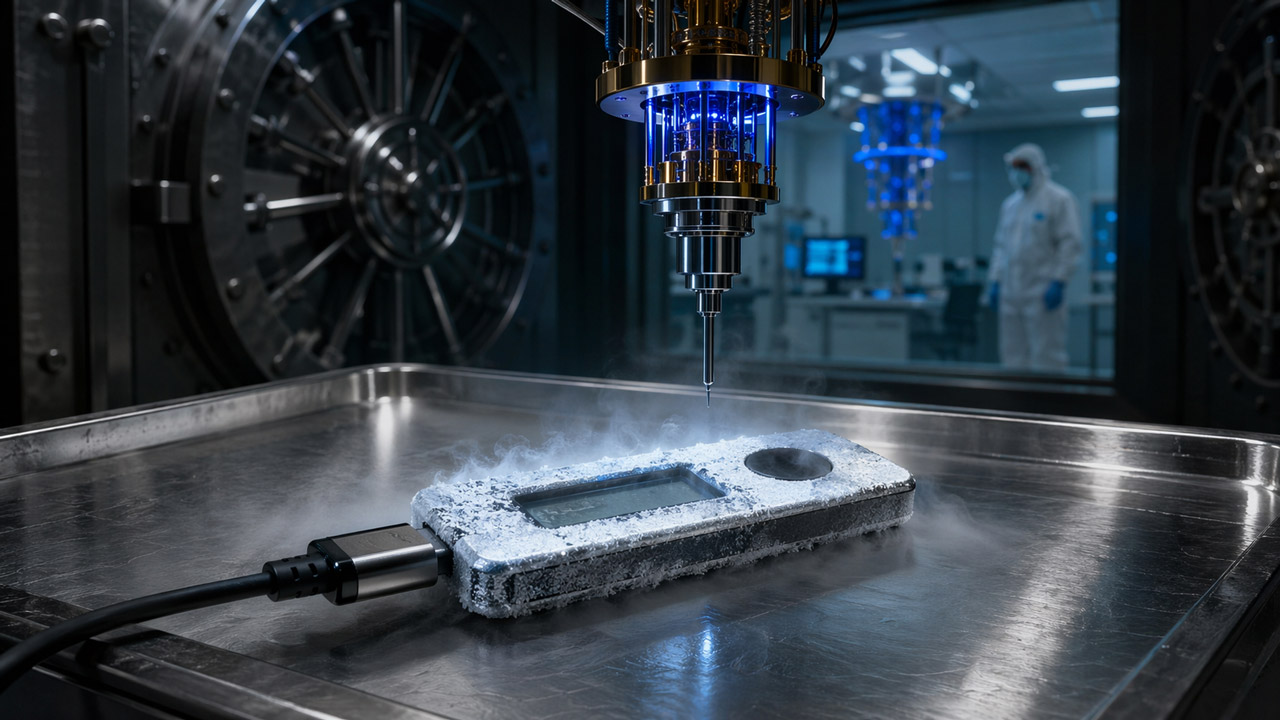
Security Vulnerabilities: The Emergence of Fraudulent Applications
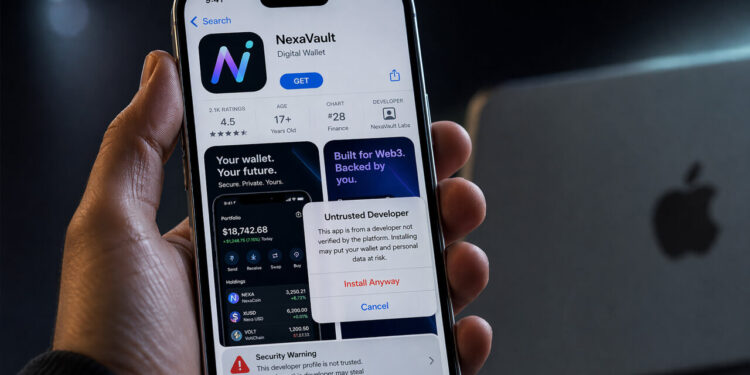
Apple has historically positioned its App Store as a rigorously managed marketplace, characterized by stringent screening protocols prior to app release. However, this reputation is now under considerable scrutiny due to recent revelations by cybersecurity researchers regarding a proliferation of fraudulent cryptocurrency wallet applications infiltrating Apple’s ecosystem. Such vulnerabilities have resulted in considerable financial losses for users.
Kaspersky Threat Research reported identifying at least 26 applications impersonating prominent cryptocurrency brands such as MetaMask, Ledger, Trust Wallet, and Coinbase. While some fraudulent apps have been expunged from circulation, others remained available at the time Kaspersky disseminated its findings. This operation was linked to a malware campaign dubbed SparkKitty, which has purportedly been active since late 2025.
The modus operandi of this scam involves initially benign applications that masquerade as innocuous tools—such as calculators or task managers—thus circumventing early detection during Apple’s review process. Once installed, these applications redirect users to webpages that mimic official App Store listings.
Sergey Puzan, a mobile malware expert at Kaspersky stated: “While the apps that kick off the attack chain are not inherently malicious, they lead to the user installing a trojan in the end. By paying a fee and setting up a developer account, the attackers can target any iOS device if the user succumbs to the phishing tactic.”
The Impact of Social Engineering and Custom Developer Profiles
This sophisticated scheme relies heavily on social engineering tactics and custom developer profiles that enable software installation outside typical App Store channels. Upon user approval of these profiles, compromised versions of cryptocurrency wallets are surreptitiously installed on affected devices. Alarmingly, reports indicate that these fraudulent applications have already inflicted substantial financial damage on unsuspecting users.
Notably, recent incidents have highlighted the vulnerability inherent within Apple’s ecosystem; American musician G. Love disclosed losing approximately $436,000 after downloading what he believed was a legitimate Ledger application from Apple’s App Store. The application prompted him to enter his seed phrase, resulting in immediate disappearance of funds.
Apple’s Dilemma: Navigating Crypto Engagement
Historically, Apple has not aggressively engaged in cryptocurrency markets; it does not maintain Bitcoin assets on its balance sheet nor does it accept cryptocurrency directly for transactions on its platform. Nonetheless, Apple has not entirely distanced itself from crypto infrastructure.
– **Technical Integration**: Software tools such as Apple CryptoKit facilitate secure cryptographic functions across devices.
– **Payment Integration**: Apple Pay interacts with elements of the cryptocurrency economy through third-party services facilitating transitions between digital assets and traditional payment mechanisms.
In recent months, Apple has relaxed certain restrictions surrounding crypto-related applications by eliminating prior limitations on specific in-app transactions involving digital assets and waiving its standard commission on these transactions. This policy shift has fostered a broader range of crypto products on its platform but has simultaneously augmented opportunities for fraudulent activities.
Enforcement Efforts Amid Growing Fraud Risks
Despite these challenges, Apple continues to tout its robust enforcement measures; it reported preventing over $9 billion in potentially fraudulent transactions between 2020 and 2024. In the preceding year alone (2024), it rejected approximately two million app submissions grounded in privacy and security concerns while terminating nearly 300,000 developer accounts due to fraud risk.
A New Chief Executive Faces Security Scrutiny
For John Ternus, assuming leadership during this tumultuous period presents formidable challenges. His reputation is built upon hardware execution and operational efficiency; however, he must now address pressing concerns regarding trust within the App Store amidst escalating incidents of organized cryptocurrency theft.
The integrity of Apple’s esteemed reputation—predicated upon the notion that its controlled environment provides superior software distribution security compared to rival platforms—is jeopardized by these burgeoning threats targeting users who predominantly rely on Apple’s vetting processes as their primary defense mechanism against fraud.
Ternus will commence his tenure under intense scrutiny from investors who will be observing not only Apple’s trajectory concerning product development and artificial intelligence strategy but also its decisive response to the increasing exploitation of its platform by organized cybercriminals engaged in cryptocurrency theft.